Homelab security becomes urgent the first time you think, “I’ll just open a port so I can check this from my phone.” That one decision is how a fun weekend project turns into a public internet server.
The goal of this guide is not paranoia. It’s boring safety. You want a setup where most mistakes are recoverable, and where exposure is always deliberate.
In this post you’ll get:
- A simple threat model for a home lab
- A safe default for remote access
- A checklist you can apply to every self-hosted app
If you are following the beginner series, this builds on earlier foundations in the Self-Hosting category.
Table of Contents
Homelab security rule #1: start local-only
If you are new, keep your first services accessible only on your LAN.
Local-only removes 80% of the risk because the public internet cannot reach your app in the first place.
A practical way to enforce this is to avoid router port forwarding until you have a clear reason and a plan.
Rule #2: assume scans are constant (because they are)
The internet is not a quiet place. If you expose a port, it will be scanned.
You do not need a personal enemy. You just need to be discoverable.
So a good mental shift is:
- “If I expose this, it will be hit by automated login attempts.”
That one assumption makes your next decisions much saner.
Rule #3: avoid random port forwarding
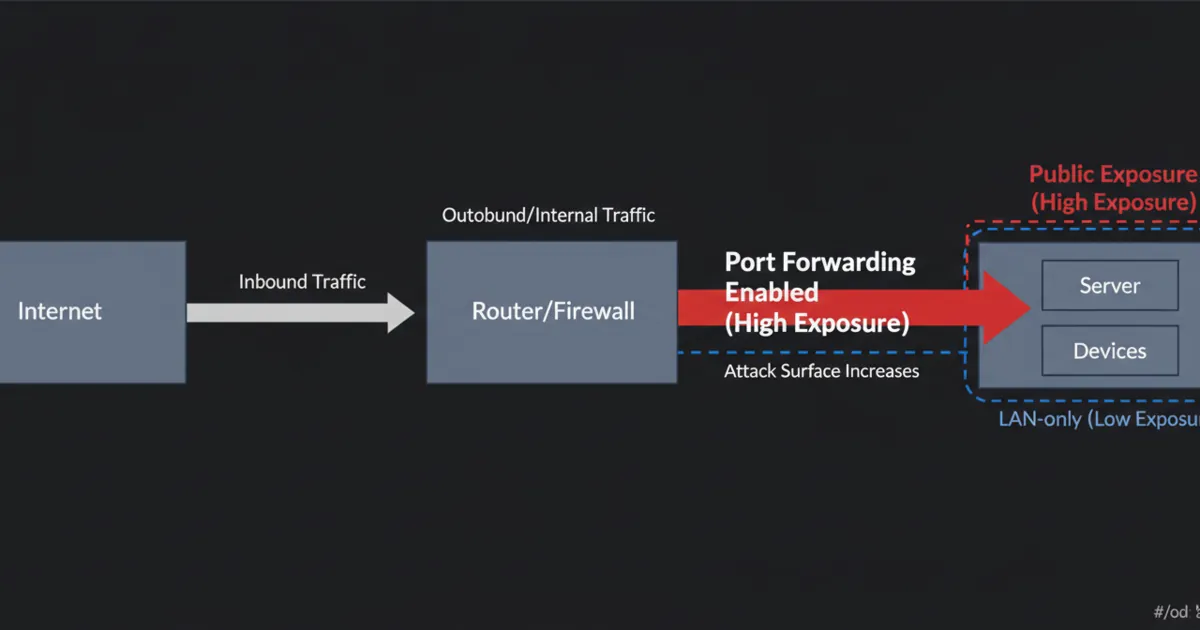
Port forwarding tells your router to send traffic from the public internet to an internal device.
Beginners often do this for a dashboard, a NAS UI, or a media server. It works, but it also creates a public target.
If you *must* port forward, prefer a single hardened entry point (like a reverse proxy on 80/443 with HTTPS and auth) rather than exposing a bunch of app ports.
Rule #4: use VPN-first remote access
For most people, the safest default is:
- VPN for you
- no public exposure for apps
A VPN makes your remote device feel like it is on your home network, without publishing your apps to the world.
References:
- WireGuard: https://www.wireguard.com/
- Tailscale (WireGuard-based): https://tailscale.com/kb/
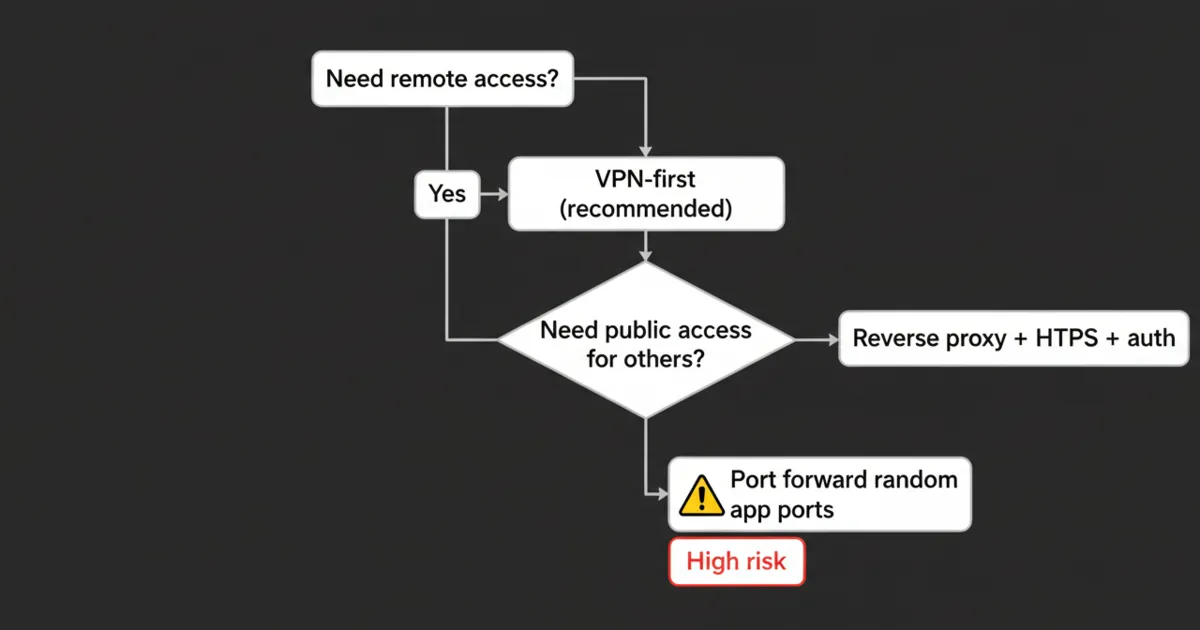
Rule #5: if you expose anything publicly, put it behind HTTPS and authentication
If you decide a service must be reachable by others (or you want a public endpoint), treat it like a real production service.
Minimum baseline:
- HTTPS
- strong authentication (and ideally multi-factor)
- rate limiting where possible
References:
- Let’s Encrypt: https://letsencrypt.org/
- OWASP Authentication Cheat Sheet: https://cheatsheetseries.owasp.org/cheatsheets/Authentication_Cheat_Sheet.html
If you are tempted to expose an admin UI, stop and ask if a VPN would solve the same need.
Rule #6: keep the host boring and patched
Most homelab security failures are not “someone hacked Docker.” They are old services, default passwords, and unpatched software.
A boring routine is powerful:
- patch the OS
- update containers intentionally
- remove services you no longer use
If you are running Linux, basic SSH hardening is worth it:
- keys only (no password SSH)
- disable root login over SSH
- allow SSH only from your LAN or VPN subnet if possible
Rule #7: reduce blast radius with segmentation (only when you are ready)
You do not need VLANs on day one, but the idea matters.
Segmentation means risky or noisy devices do not sit on the same network as your servers.
A beginner-friendly progression:
- Start with one stable LAN.
- When you have time, create a separate network for IoT devices.
- Keep the homelab server network more restricted.
This is homelab security in practice: even if one device gets compromised, it is harder to pivot to everything else.
Rule #8: use one hardened front door (reverse proxy) instead of many open ports
If you decide something must be reachable over the internet, do not expose ten different app ports.
Use one entry point:
- reverse proxy
- HTTPS
- authentication
- optional IP allowlists
This keeps your exposure auditable. You can point to one place and say, “This is what is public.”
Rule #9: treat credentials like the real security boundary
A lot of homelab security comes down to identity.
Practical defaults:
- unique passwords
- a password manager
- turn on MFA where you can
- do not reuse your router password anywhere
If you run a reverse proxy with basic auth, make sure it is not your only defense for something truly sensitive.
Rule #10: block brute force and alert on weird login behavior
If something is public, you should assume it will be hammered.
At minimum, you want:
- rate limiting at the reverse proxy
- account lockouts where supported
- log visibility
Even simple protections reduce the chance that a weak password becomes your entire homelab security story.
Rule #11: backups are a security feature
Security is not only about preventing break-ins. It is also about surviving failure.
You want to be able to recover from:
- a bad update
- a disk failure
- ransomware on a client device
A simple rule:
- if you cannot restore it, you do not really own it
Rule #12: audit your exposure regularly
A surprisingly effective homelab security habit is an exposure audit.
Once a month, ask:
- What ports are forwarded on my router?
- What DNS names point to my home IP?
- What services are intended to be public?
If you cannot explain why a port is open, close it and re-open only when you have time to verify.
Rule #13: monitor the boring signals
Beginners usually notice problems only when something is down.
You want to notice earlier:
- unexpected login attempts
- sudden spikes in traffic
- a new port open on your router
Lightweight monitoring is enough at first. Even uptime checks plus basic logs are a big upgrade.
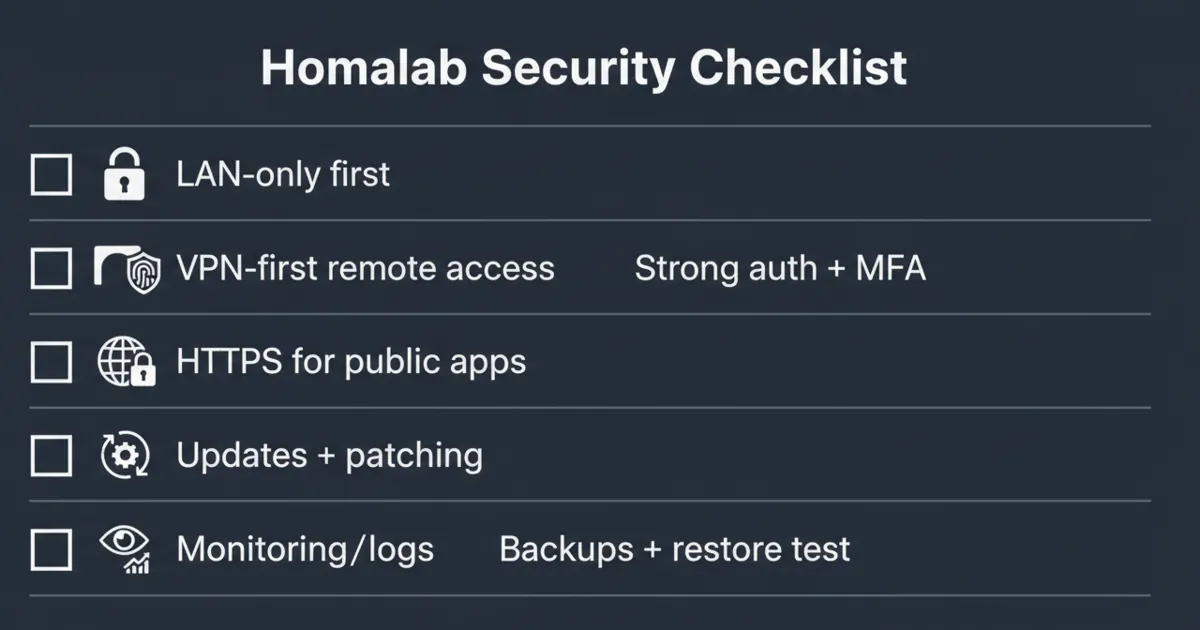
A simple homelab security checklist (use this per app)
Before you expose or rely on a service, verify:
- Is it LAN-only by default?
- Where do the data and config live?
- Do you have a restore path?
- Is authentication strong?
- Are updates manageable?
- Is it behind a single entry point (VPN or reverse proxy) instead of many open ports?
- Does it run with the least privileges possible (no extra admin access, no unnecessary mounts)?
Least privilege sounds advanced, but the homelab version is simple: do not give a container or app access to parts of the system it does not need. Every permission you remove is one less way a mistake turns into a full takeover.
FAQ
Is port forwarding always unsafe for homelab security?
Not always, but it is high-risk for beginners. If you do it, reduce the number of exposed services and harden the one entry point you publish.
What is the safest way to access my homelab remotely?
VPN-first is the safest default for most people. It avoids exposing app ports and keeps access limited to your devices.
Should I expose Jellyfin, Home Assistant, or my NAS UI to the internet?
Generally no, not directly. If you need remote access, use a VPN. If you need public access for others, use a reverse proxy with strong auth and HTTPS.
I only want to expose one service. What is the least risky way?
Expose one reverse proxy over HTTPS and put the service behind authentication, instead of forwarding the app port directly. If the service is only for you, VPN is still simpler and safer.
Do I need VLANs and a DMZ for homelab security?
Not at first. They are helpful once you understand your normal LAN well, but good defaults, VPN-first access, and fewer exposed services deliver most of the safety.
How do I know if I accidentally exposed something?
Start with your router’s port forwards. Then check what services are listening, and what you intended to publish. If you are unsure, remove forwards and re-add only what you can explain.
What is the one thing beginners forget?
Backups and restore tests. If you cannot restore, a bad update or compromise can become permanent data loss.
Next steps
Pick one improvement today:
- Remove any port forwards you do not 100% understand
- Set up VPN for remote access
- Turn on MFA on your most important accounts
- Write down backup and restore steps for one service
Homelab security is not about being perfect. It is about making exposure deliberate and recovery easy.


2 Comments
Pingback: Nextcloud vs Seafile vs Syncthing: Which One Should You Self-Host? - HomeLabAddiction
Pingback: Immich vs PhotoPrism (2026): I Switched - Here's What I Learned - HomeLabAddiction